Firmware
Tesla patches security hole ahead of Version 8 Autopilot OTA update

Tesla Model S and Model X owners woke up to a surprise over-the-air (OTA) software update on Monday, days ahead of the company’s much-anticipated Version 8 software that promises an improved Autopilot system centered around radar technology. However, contrary to what owners were hoping for, it wasn’t v8.0. Instead, the company issued an update to existing Firmware v7.1 (2.36.31) after Chinese security firm Keen exposed a vulnerability that would allow attackers to remotely activate a vehicle’s brakes while the car is in motion.
Beyond being able to compromise one of the driving functions of the vehicle, researchers from Keen Security Lab were able to hack a new Model S 75D and remotely present the vehicle’s door handles, allowing a would-be thief to gain access to the interior of the car. The researchers exploited a search function from Tesla’s onboard web browser that would allow them to take control of the car and open the vehicle’s trunk, fold the mirrors while the car is in motion, move the power seats, as well as completely disable all touch controls from the main infotainment system.
Though the circumstances leading to a Model S or Model X to be hacked would be rare – it requires the driver to connect to a malicious WiFi network that the hacker has access to – the discovery highlights the inherent vulnerabilities with having a connected car.
Tesla quickly patched the security holes through an OTA update after working with Keen on addressing the issues. The company released the following statement to The Verge explaining details behind its recent v7.1 update:
Within just 10 days of receiving this report, Tesla has already deployed an over-the-air software update (v7.1, 2.36.31) that addresses the potential security issues. The issue demonstrated is only triggered when the web browser is used, and also required the car to be physically near to and connected to a malicious wifi hotspot. Our realistic estimate is that the risk to our customers was very low, but this did not stop us from responding quickly.
We engage with the security research community to test the security of our products so that we can fix potential vulnerabilities before they result in issues for our customers. We commend the research team behind today’s demonstration and plan to reward them under our bug bounty program, which was set up to encourage this type of research.
Tesla’s level of commitment to work with independent researchers and the general community on improving security (through a bug bounty program) is another great example on why this Silicon Valley automaker is serious about security and stands miles apart from other automakers.
Check out the demonstration video from Keen Security Lab showing a Model S being compromised.
Elon Musk
Tesla confirmed HW3 can’t do Unsupervised FSD but there’s more to the story
Tesla confirmed HW3 vehicles cannot run unsupervised FSD, replacing its free upgrade promise with a discounted trade-in.

Tesla has officially confirmed that early vehicles with its Autopilot Hardware 3 (HW3) will not be capable of unsupervised Full Self-Driving, while extending a path forward for legacy owners through a discounted trade-in program. The announcement came by way of Elon Musk in today’s Tesla Q1 2026 earnings call.
🚨 Our LIVE updates on the Tesla Earnings Call will take place here in a thread 🧵
Follow along below: pic.twitter.com/hzJeBitzJU
— TESLARATI (@Teslarati) April 22, 2026
The history here matters. HW3 launched in April 2019, and Tesla sold Full Self-Driving packages to owners on the understanding that the hardware was sufficient for full autonomy. Some owners paid between $8,000 and $15,000 for FSD during that period. For years, as FSD’s AI models grew more demanding, HW3 vehicles fell progressively further behind, eventually landing on FSD v12.6 in January 2025 while AI4 vehicles moved to v13 and then v14. When Musk acknowledged in January 2025 that HW3 simply could not reach unsupervised operation, and alluded to a difficult hardware retrofit.
The near-term offering is more concrete. Tesla’s head of Autopilot Ashok Elluswamy confirmed on today’s call that a V14-lite will be coming to HW3 vehicles in late June, bringing all the V14 features currently running on AI4 hardware. That is a meaningful software update for owners who have been frozen at v12.6 for over a year, and it represents genuine effort to keep older hardware relevant. Unsupervised FSD for vehicles is now targeted for Q4 2026 at the earliest, with Musk describing it as a gradual, geography-limited rollout.
For HW3 owners, the over-the-air V14-lite update is welcomed, and the discounted trade-in path at least acknowledges an old obligation. What happens next with the trade-in pricing will define how this chapter ultimately gets written. If Tesla prices the hardware path fairly, acknowledges what early adopters are owed, and delivers V14-lite on the June timeline it committed to today, it has a real opportunity to convert one of the longest-running sore subjects among early adopters into a loyalty story.
Firmware
Tesla 2026 Spring Update drops 12 new features owners have been waiting for
Tesla announced its Spring 2026 software update, and it’s the most feature-dense seasonal release the company has put out. The update covers twelve named changes spanning FSD, voice AI, safety lighting, dashcam storage, and pet display customization, among other things.
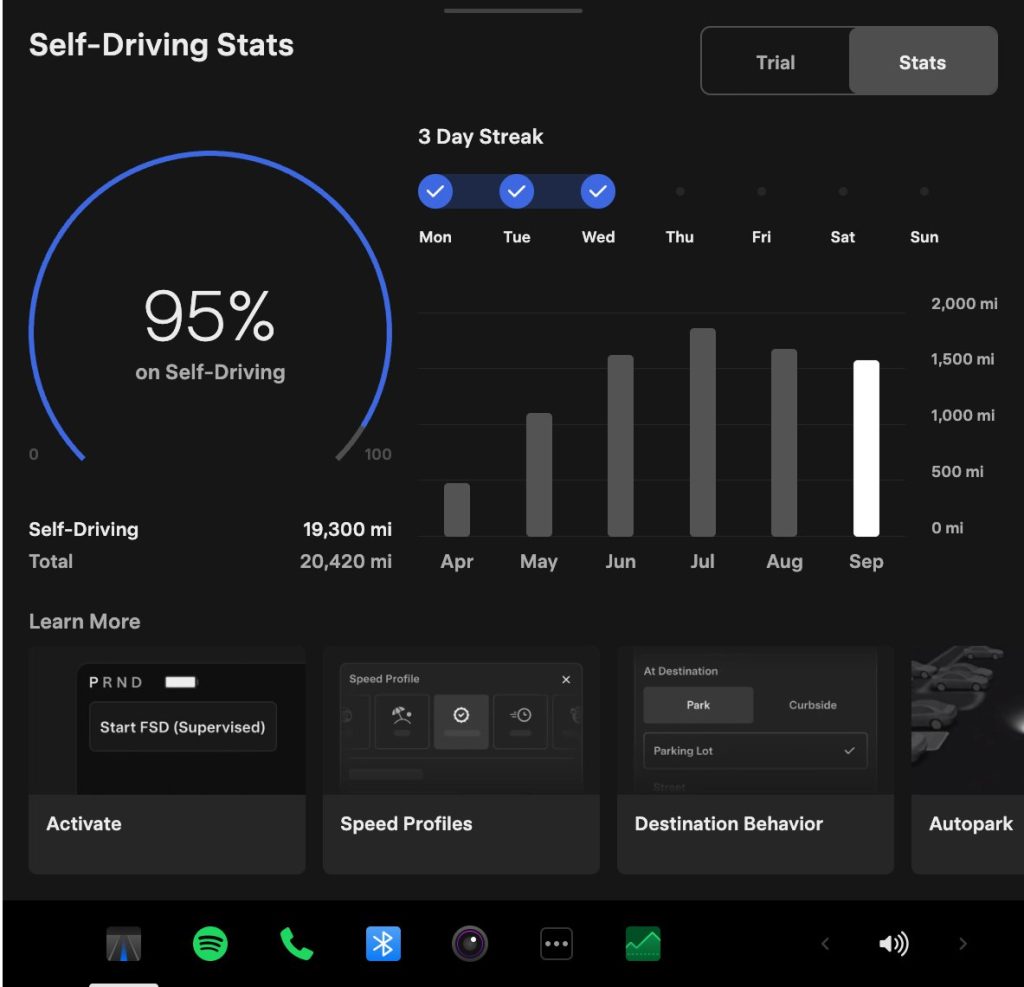
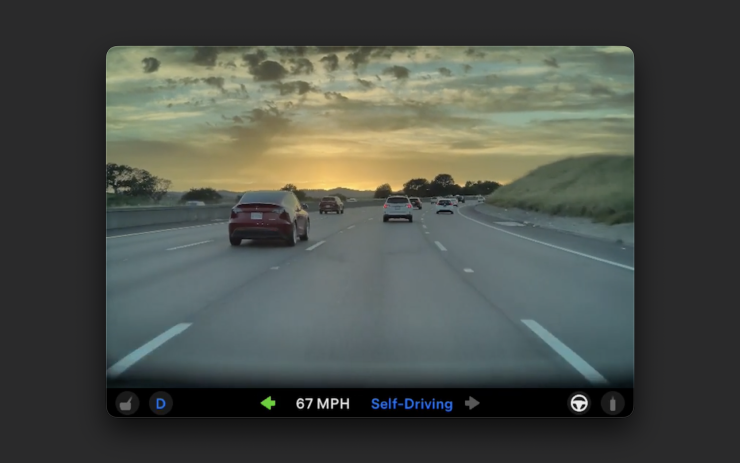
The centerpiece for owners with AI4 hardware is a redesigned Self-Driving app. The new interface lets owners subscribe to Full Self-Driving with a single tap and view ongoing FSD usage stats directly in the vehicle.
Grok gets its biggest in-car upgrade yet. The update adds a “Hey Grok” hands-free wake word along with location-based reminders, so a driver can now say “remind me to pick up groceries when I get home” without touching the screen. Grok first arrived in vehicles in July 2025, but each update has pushed it closer to genuine daily utility. Musk framed the broader vision clearly at Davos in January, saying Tesla is “really moving into a future that is based on autonomy.”
On safety, the update introduces enhanced blind spot warning lights that integrate directly with the cabin’s ambient lighting, building on the blind spot door warning that arrived in update 2026.8.
Dog Mode has been renamed Pet Mode and now lets owners choose a dog, cat, or hedgehog icon and add their pet’s name to the display.
Dashcam retention now extends up to 24 hours, up from the previous one-hour rolling loop, with a permanent save option for any clip. Weather maps now show rain and snow with better color differentiation and include the past hour of precipitation data along the route.
Tesla has now established a clear rhythm of two major OTA pushes per year. As with last year’s Spring update, that cycle started taking shape in 2025 with adaptive headlights and trunk customization. The 2025 Holiday Update then added Grok to the vehicle for the first time. This Spring follows that structure: the Holiday update introduces new architecture, and the Spring update broadens it across the fleet.
Two notable features still did not make it. IFTTT automations, which launched in China earlier this year, were held back from this North American release for unknown reasons, and Apple CarPlay remains absent, reportedly still delayed by iOS 26 and Apple Maps compatibility issues.
Below is the full list of feature updates released by Tesla.
— Tesla (@Tesla) April 13, 2026
Firmware
Tesla mobile app shows signs of upcoming FSD subscriptions

It appears that Tesla may be preparing to roll out some subscription-based services soon. Based on the observations of a Wales-based Model 3 owner who performed some reverse-engineering on the Tesla mobile app, it seems that the electric car maker has added a new “Subscribe” option beside the “Buy” option within the “Upgrades” tab, at least behind the scenes.
A screenshot of the new option was posted in the r/TeslaMotors subreddit, and while the Tesla owner in question, u/Callump01, admitted that the screenshot looks like something that could be easily fabricated, he did submit proof of his reverse-engineering to the community’s moderators. The moderators of the r/TeslaMotors subreddit confirmed the legitimacy of the Model 3 owner’s work, further suggesting that subscription options may indeed be coming to Tesla owners soon.
Did some reverse engineering on the app and Tesla looks to be preparing for subscriptions? from r/teslamotors
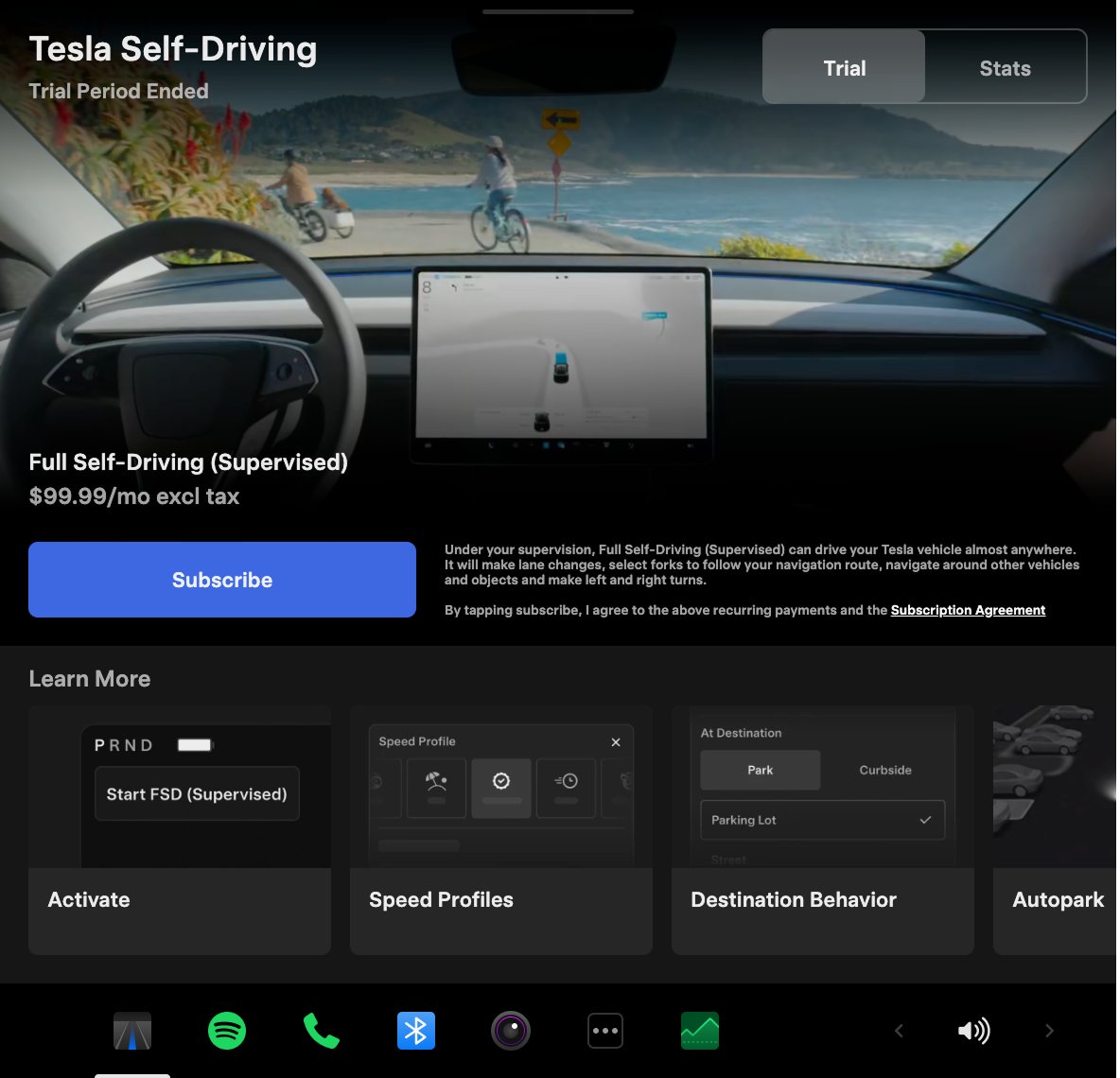
Tesla’s Full Self-Driving suite has been heavily speculated to be offered as a subscription option, similar to the company’s Premium Connectivity feature. And back in April, noted Tesla hacker @greentheonly stated that the company’s vehicles already had the source codes for a pay-as-you-go subscription model. The Tesla hacker suggested then that Tesla would likely release such a feature by the end of the year — something that Elon Musk also suggested in the first-quarter earnings call. “I think we will offer Full Self-Driving as a subscription service, but it will be probably towards the end of this year,” Musk stated.
While the signs for an upcoming FSD subscription option seem to be getting more and more prominent as the year approaches its final quarter, the details for such a feature are still quite slim. Pricing for FSD subscriptions, for example, have not been teased by Elon Musk yet, though he has stated on Twitter that purchasing the suite upfront would be more worth it in the long term. References to the feature in the vehicles’ source code, and now in the Tesla mobile app, also listed no references to pricing.
The idea of FSD subscriptions could prove quite popular among electric car owners, especially since it would allow budget-conscious customers to make the most out of the company’s driver-assist and self-driving systems without committing to the features’ full price. The current price of the Full Self-Driving suite is no joke, after all, being listed at $8,000 on top of a vehicle’s cost. By offering subscriptions to features like Navigate on Autopilot with automatic lane changes, owners could gain access to advanced functions only as they are needed.
Elon Musk, for his part, has explained that ultimately, he still believes that purchasing the Full Self-Driving suite outright provides the most value to customers, as it is an investment that would pay off in the future. “I should say, it will still make sense to buy FSD as an option as in our view, buying FSD is an investment in the future. And we are confident that it is an investment that will pay off to the consumer – to the benefit of the consumer.” Musk said.