News
Chinese Find Obvious Tesla Model S Security Flaw

 A group of Chinese hacker reported that the Model S has a security flaw. We say, welcome to reality. Any system that is connected, whether physical or wireless, has a potential security flaw.
A group of Chinese hacker reported that the Model S has a security flaw. We say, welcome to reality. Any system that is connected, whether physical or wireless, has a potential security flaw.
Model S has a security flaw
The Tesla Model S security flaw is making its round lately. It has to make you wonder when reports on security exploits related to computer systems appear. Modern computers, including cars and their wireless technologies have many open ports and channels. A long, long time ago, when I was learning about Novell servers, (yes, I’m that old) my teacher taught me that a truly un-hackable computer is one without a mouse, keyboard or Internet connection. It helped to understand that once a port is open, either with a keyboard of wireless connection, even if secured, there is still a potential vulnerability.
The Model S open connections mean potential security flaw
The Model S is not really a car. It’s more of a future template of what every car will soon look like. It is more of a rolling computer on wheels, which handles quite well. But the Tesla Model S is always connected, either to Tesla Motors, or the Internet, as well as many other types communication is happening. What this means is that the Model S is, by definition, as vulnerable as its weakest point in the security chain. So is it any wonder to hear that the Model S, the most Internet-connected and remotely-connected electric vehicle (EV) on the market today, has a major security flaw? It shouldn’t. Anything connected cars, even Tesla’s Model S means it can be hacked and has security flaws.
According to TransportEvolved, Sina Weibo announced a Chinese Internet security company called Qihoo 360, found Tesla Model S security flaw. This is one of the most common security issue with anything connected and it means a crafty hacker can remotely access and unlock your Tesla Model S, as well as sound the horns, use the headlights, wipers, and even the panoramic sunroof. Are you scared yet? At the very least, if it rains, you might get annoyed.
Making sense of the Tesla Model S security flaw
Once we take a few steps back, we can see a pattern emerging from this Tesla Model S security flaw news. First, it was announced a day before one of the biggest security conference in China, the 2014 SyScan +360. Add to this that the conference is awarding a $10,000 prize to whoever successfully hacks into a Tesla Model S, and you get a better picture of what is happening. The Tesla Motors Model S is as secured as can be, and will continue to be more secured as each individual security flaws are discovered.
Tesla Motors was quick to reassure us with the following: “While Tesla is not associated with the conference and is not a sponsor of the competition, we support the idea of providing an environment in which responsible security researchers can help identify potential vulnerabilities. We hope that the security researchers will act responsibly and in good faith.” Whether open or closed sources, nothing is 100% secured if it is connected.
But joking apart, news of the Tesla Model S security flaw is a welcome relief in a world of over-confidence and side-blinders. In the meantime, as user and hacker feedback rolls in, Tesla will rewrite some APIs and take a closer look at some of the certificates it uses. So far, if sounding your horn, opening your doors and sunroof are the biggest threats, we can say that the latest Tesla Motors Model S security flaw is only a potential… so far.
Elon Musk
Tesla investors will be shocked by Jim Cramer’s latest assessment
Jim Cramer is now speaking positively about Tesla, especially in terms of its Robotaxi performance and its perception as a company.

Tesla investors will be shocked by analyst Jim Cramer’s latest assessment of the company.
When it comes to Tesla analysts, many of them are consistent. The bulls usually stay the bulls, and the bears usually stay the bears. The notable analysts on each side are Dan Ives and Adam Jonas for the bulls, and Gordon Johnson for the bears.
Jim Cramer is one analyst who does not necessarily fit this mold. Cramer, who hosts CNBC’s Mad Money, has switched his opinion on Tesla stock (NASDAQ: TSLA) many times.
He has been bullish, like he was when he said the stock was a “sleeping giant” two years ago, and he has been bearish, like he was when he said there was “nothing magnificent” about the company just a few months ago.
Now, he is back to being a bull.
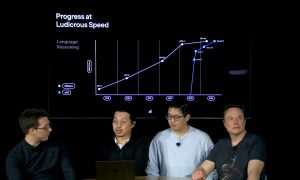
Cramer’s comments were related to two key points: how NVIDIA CEO Jensen Huang describes Tesla after working closely with the Company through their transactions, and how it is not a car company, as well as the recent launch of the Robotaxi fleet.
Jensen Huang’s Tesla Narrative
Cramer says that the narrative on quarterly and annual deliveries is overblown, and those who continue to worry about Tesla’s performance on that metric are misled.
“It’s not a car company,” he said.
He went on to say that people like Huang speak highly of Tesla, and that should be enough to deter any true skepticism:
“I believe what Musk says cause Musk is working with Jensen and Jensen’s telling me what’s happening on the other side is pretty amazing.”
Tesla self-driving development gets huge compliment from NVIDIA CEO
Robotaxi Launch
Many media outlets are being extremely negative regarding the early rollout of Tesla’s Robotaxi platform in Austin, Texas.
There have been a handful of small issues, but nothing significant. Cramer says that humans make mistakes in vehicles too, yet, when Tesla’s test phase of the Robotaxi does it, it’s front page news and needs to be magnified.
He said:
“Look, I mean, drivers make mistakes all the time. Why should we hold Tesla to a standard where there can be no mistakes?”
It’s refreshing to hear Cramer speak logically about the Robotaxi fleet, as Tesla has taken every measure to ensure there are no mishaps. There are safety monitors in the passenger seat, and the area of travel is limited, confined to a small number of people.
Tesla is still improving and hopes to remove teleoperators and safety monitors slowly, as CEO Elon Musk said more freedom could be granted within one or two months.
News
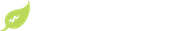
Tesla launches ultra-fast V4 Superchargers in China for the first time
Tesla has V4 Superchargers rolling out in China for the first time.
Tesla already has nearly 12,000 Supercharger piles across mainland China. However, the company just initiated the rollout of the ultra-fast V4 Superchargers in China for the first time, bringing its quick-charging piles to the country for the first time since their launch last year.
The first batch of V4 Superchargers is now officially up and running in China, the company announced in a post on Chinese social media outlet Weibo today.
The company said in the post:
“The first batch of Tesla V4 Superchargers are online. Covering more service areas, high-speed charging is more convenient, and six-layer powerful protection such as rain and waterproof makes charging very safe. Simultaneously open to non-Tesla vehicles, and other brands of vehicles can also be charged. There are more than 70,000 Tesla Superchargers worldwide. The charging network layout covers 100% of the provincial capitals and municipalities in mainland China. More V4 Superchargers will be put into use across the country. Optimize the charging experience and improve energy replenishment efficiency. Tesla will accompany you to the mountains, rivers, lakes, and seas with pure electricity!”
The first V4 Superchargers Tesla installed in China are available in four cities across the country: Shanghai, Zhejiang, Gansu, and Chongqing.

Credit: Tesla China
Tesla has over 70,000 Superchargers worldwide. It is the most expansive and robust EV charging network in the world. It’s the main reason why so many companies have chosen to adopt Tesla’s charging connector in North America and Europe.
In China, some EVs can use Tesla Superchargers as well.
The V4 Supercharger is capable of charging vehicles at speeds of up to 325kW for vehicles in North America. This equates to over 1,000 miles per hour of charging.
Elon Musk
Elon Musk hints at when Tesla could reduce Safety Monitors from Robotaxi
Tesla could be reducing Safety Monitors from Robotaxi within ‘a month or two,’ CEO Elon Musk says.

Elon Musk hinted at when Tesla could begin reducing Safety Monitors from its Robotaxis. Safety Monitors are Tesla employees who sit in the front passenger seat during the driverless rides, and are there to ensure safety for occupants during the earliest rides.
Tesla launched its Robotaxi fleet in Austin last Sunday, and after eight days, videos and reviews from those who have ridden in the driverless vehicles have shown that the suite is safe, accurate, and well coordinated. However, there have been a few hiccups, but nothing that has put anyone’s safety in danger.
A vast majority — close to all of the rides — at least according to those who have ridden in the Robotaxi, have been performed without any real need for human intervention. We reported on what was the first intervention last week, as a Safety Monitor had to step in and stop the vehicle in a strange interaction with a UPS truck.
Watch the first true Tesla Robotaxi intervention by safety monitor
The Tesla and UPS delivery truck were going for the same street parking space, and the Tesla began to turn into it. The UPS driver parallel parked into the spot, which was much smaller than his truck. It seemed to be more of an instance of human error instead of the Robotaxi making the wrong move. This is something that the driverless cars will have to deal with because humans are aggressive and sometimes make moves they should not.
The Safety Monitors have not been too active in the vehicles. After all, we’ve only seen that single instance of an intervention. There was also an issue with the sun, when the Tesla braked abnormally due to the glare, but this was an instance where the car handled the scenario and proceeded normally.
With the Robotaxi fleet operating impressively, some are wondering when Tesla will begin scaling back both the Safety Monitors and Teleoperators that it is using to ensure safety with these early rides.
CEO Elon Musk answered the inquiry by stating, “As soon as we feel it is safe to do so. Probably within a month or two.”
As soon as we feel it is safe to do so.
Probably within a month or two. We continue to improve the Tesla AI with each mile driven.
— Elon Musk (@elonmusk) June 30, 2025
Musk’s response seems to confirm that there will be fewer Teleoperators and Safety Monitors in the coming months, but there will still be some within the fleet to ensure safety. Eventually, that number will get to zero.
Reaching a point where Tesla’s Robotaxi is driverless will be another significant milestone for the company and its path to fully autonomous ride-sharing.
Eventually, Tesla will roll out these capabilities to consumer-owned vehicles, offering them a path to generate revenue as their car operates autonomously and completes rides.
For now, Tesla is focusing on perfecting the area of Austin where it is currently offering driverless rides for just $4.20 to a small group of people.
-

 News5 days ago
News5 days agoTesla Robotaxi’s biggest challenge seems to be this one thing
-

 News2 weeks ago
News2 weeks agoTesla confirms massive hardware change for autonomy improvement
-
 Elon Musk2 weeks ago
Elon Musk2 weeks agoElon Musk slams Bloomberg’s shocking xAI cash burn claims
-

 News2 weeks ago
News2 weeks agoTesla features used to flunk 16-year-old’s driver license test
-

 News2 weeks ago
News2 weeks agoTesla China roars back with highest vehicle registrations this Q2 so far
-

 News2 weeks ago
News2 weeks agoTexas lawmakers urge Tesla to delay Austin robotaxi launch to September
-

 News2 weeks ago
News2 weeks agoTesla dominates Cars.com’s Made in America Index with clean sweep
-

 News2 weeks ago
News2 weeks agoTesla’s Grok integration will be more realistic with this cool feature